Digital Transition: The Opportunity in Cybersecurity
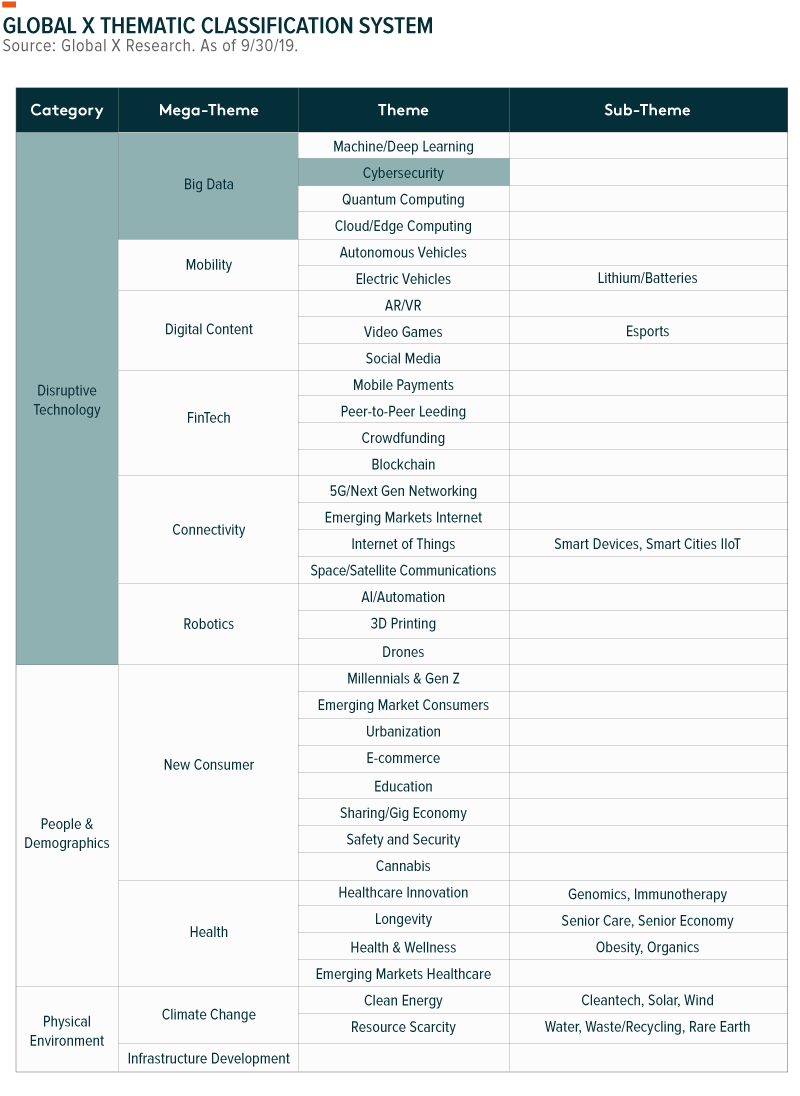
As the world becomes digitised, protecting valuable and sensitive data is increasingly essential. Technology improves productivity by bringing tangible items into the digital world and automating manual processes. However, as more items and processes leave the physical world and enter the digital realm, it opens the door for new types of crime. Damages from cybercrime could cost the world US$6tr annually by 2021, prompting individuals, companies, and governments to spend fortunes engaging with cybersecurity firms to provide sophisticated software and services to protect proprietary data.1 As such, we believe cybersecurity is a powerful theme that will be further propelled by the growth of tangential areas that produce, utilise, or offer connectivity to data, such as machine learning, cloud computing, and the internet of things.
The Rise of Big Data
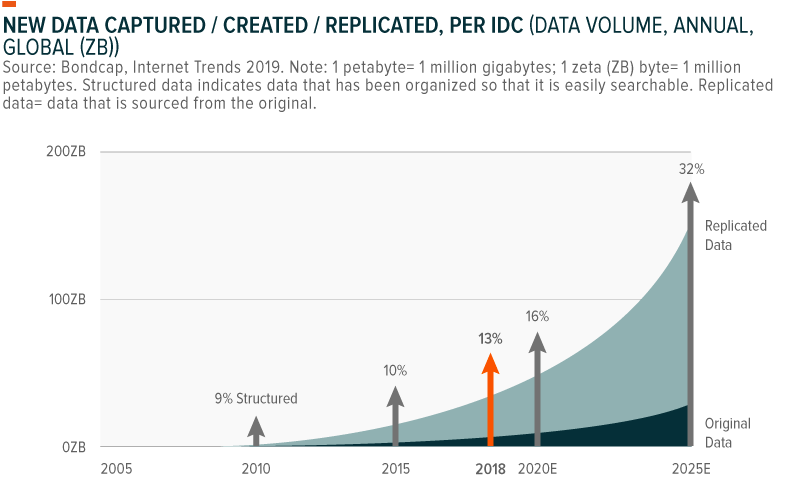
Not too long ago, file cabinets full of alphabetised folders stored critical information like addresses, health records, and financial statements. Then came computers and the internet, establishing a new digital paradigm that began to capture and store vast amounts of information in 1’s and 0’s. Seemingly overnight, technology made data readily available at the click of a mouse. Yet it didn’t stop there. Turning old data from physical records into digital ones was the first phase, but now, virtually everything we do leaves behind a digital trail: what we purchase, what we watch, who we talk to, and where we go are captured by various platforms. According to one estimate, the world generates more than 2.5 quintillion bytes (2.5×1018) of data every day, or equivalent to 90% of all data generated during the last two years.2 For another perspective, in 2020 the world is set to generate 40 times more bytes of data per day than the number of stars in the observable universe.3
Furthering this explosion in data is the emergence of a handful of digital technologies, including: 1) the internet of things, which is connecting everyday devices from dishwashers to TVs to the internet to collect and transmit data; 2) cloud computing, offering cheap, scalable, and efficient data infrastructure services that lowers the barrier for firms to become more data-dependent; and 3) machine learning and artificial intelligence, which makes data more valuable than ever before as insights can be discovered from vast data sets.
Proliferation of data = Proliferation of cyberthreats
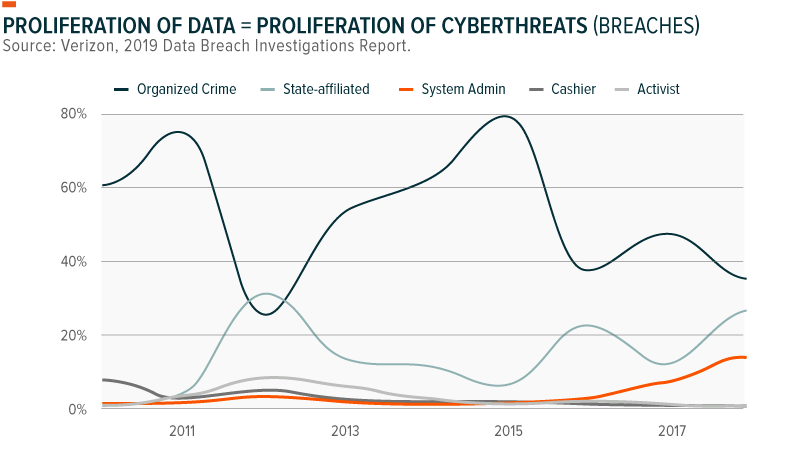
But as more valuable data is created, cybercriminals become increasingly motivated to steal it and sell the data on the black market, hold it for ransom, or expose private information. Most commonly, cybercriminals use digital means to steal proprietary or private data, intellectual property (IP), and money. Yet as technology evolves, so too will the cyberthreats. For example, as the internet of things connects everyday objects to the internet, it creates new avenues for cybercriminals to operate. Hacked traffic lights, stolen cars, or manipulated personal health devices are now all in the realm of the possible.
A single cybersecurity company can block over 100 million threats per day.4 That’s equivalent to more than one thousand threats blocked every second. But all it takes is one breach to cause severe damage for companies and users.
In 2013-14, Yahoo! had all 3 billion of its accounts hacked in two separate attacks, arguably the worst data breaches of the 21st century. The breaches exposed names, email addresses, birth dates, telephone numbers, passwords and security questions of users. Somewhat troublingly, Yahoo! confirmed the attacks in 2017, 3–4 years after the events actually happened.
In 2017, Equifax, one of the largest credit bureaus in the US, announced a data breach that affected 143 million consumers, including social security numbers, birth dates and driver’s license numbers. In late 2018, Marriott International announced a data breach that compromised 500 million accounts, including personal information like passport numbers.
Typically, external actors are the culprits of cybercrime. In the Yahoo! case, state-sponsored-actors were responsible, which is not uncommon; hackers sponsored by foreign governments account for about 23% of global breaches.5 Organised crime accounts for another 39% of data breaches.
But external actors are not the only concern. Internal breaches occur as well, committed for personal or financial gain, and sometimes simply the result of human error.
An Ecosystem of Solutions is Needed
Defending against cyberthreats is an industry. Cybersecurity services focuses on protecting all levels of a network, including gateway, identity, email, cloud, web security and endpoints. The techniques cybersecurity companies use to combat unauthorised and malicious activity vary, and can include any one or, more likely, combinations of the following:6
- Authentication & Authorisation: A process that uses permissions to identify and authenticate user activity.
- Cryptography: A process that allows mathematical functions to secure communications
- Auto-Analysis of Legitimate Usage Patterns: Automatic usage pattern analysis used to alert administrators of unusual behaviour
- Intrusion Detection & Risk Mitigation: A proactive approach that seeks to prevent malicious actors from penetrating a system
- Data Integrity Verification: Analysis to ensure data remain intact, and to assess the scope of damages or alternations made
- Computer Forensics: A reactive mechanism that traces cyberthreats and crimes to identify how and why events occurred
We expect proactive prevention mechanisms will evolve to include artificial intelligence (AI) and machine learning (ML) approaches. AI and ML can help with phishing detection, recognising fake websites and links that attempt to look as legitimate. Progress in visual recognition technology is another area where AI and ML can assist next generation cybersecurity companies detect potential threats. Of course, for AI and ML mechanisms to evolve, they need access to large amounts of data, including malignant data like malware for training purposes.
Greater Spending on Cybersecurity Warranted
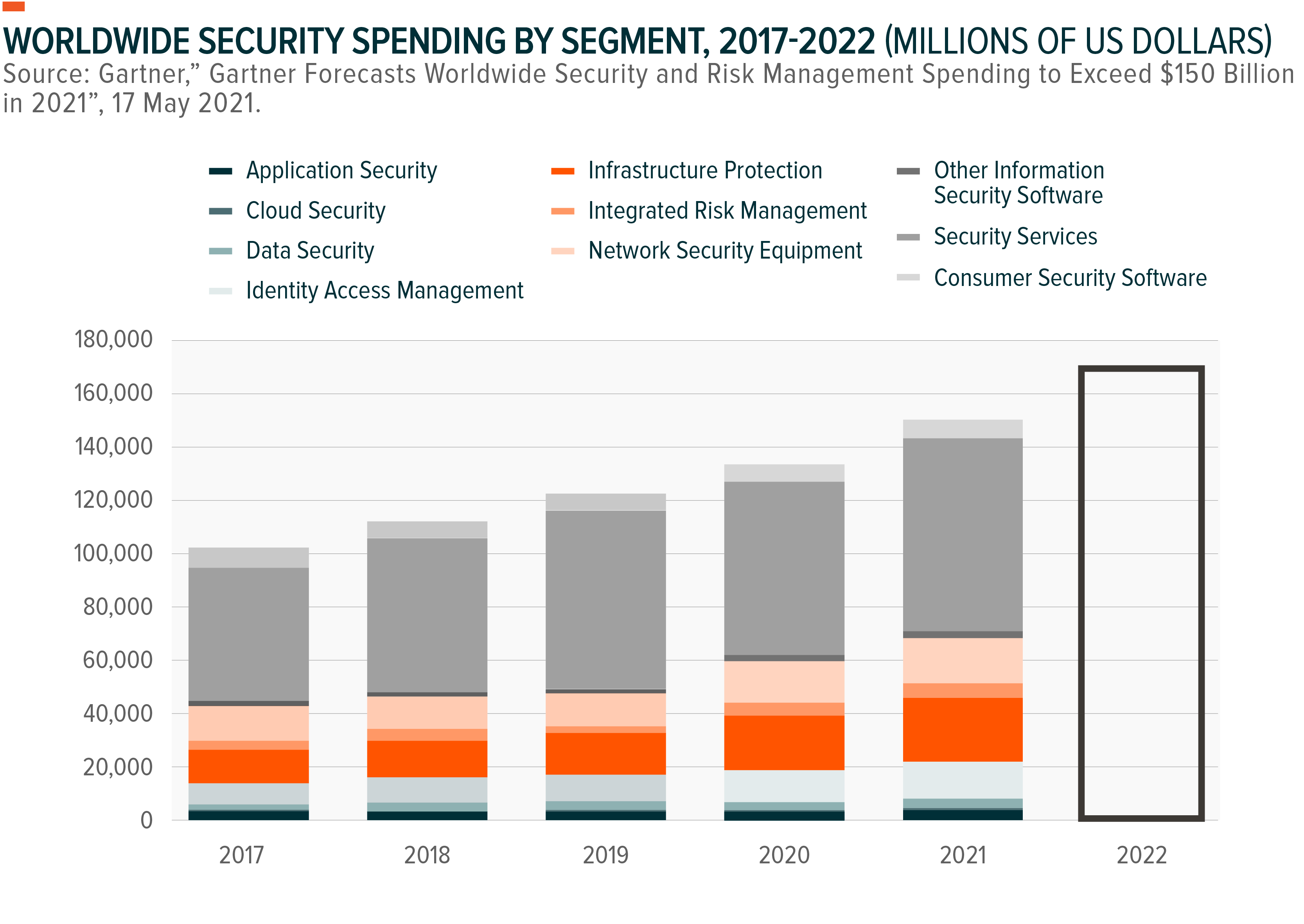
Cybersecurity is one of the fastest-growing segments of IT spending. Chief Information Officers (CIOs) across the US consistently rank cybersecurity as their top spending priority.7 And it’s understandable why companies can spend millions on cybersecurity: in 2019, the average total cost of a data breach for a company is US$3.9mn, with 36% of the cost coming from the loss of customer trust.8
Global spending on security-related software, hardware and services could reach US$124bn by year-end as the number of malicious programs registered reaches a record 925 million.9,10 By 2022, total global spending could reach US$170.4bn, a five-year compounded annual growth rate (CAGR) of 10.9%.11 Given the proliferation of cyberthreats, cybersecurity is now often viewed as a cost-savings measure for organisations who fear the costs and fallout of an attack.
Likewise, government spending on cybersecurity implementations continues to grow. The EU General Data Protection Regulation (GDPR), which went into effect in May 2018, calls for personal data to be processed in a manner that ensures security, protection and transparency.
In the U.S., cybersecurity is a priority and regulators continue to work toward GDPR-like legislation. The 2019 federal budget included US$15bn for cybersecurity, a US$583.4mn, or 4.1% percent, increase over 2018.12 Cybersecurity is a state-level issue too. California passed a digital privacy law in 2018 that grants people control over their data. Such legislation creates a sense of urgency on the corporate side to enhance their cybersecurity promptly and avoid any potential scandals.
Conclusion
Digital transformation across all industries implies that cybersecurity capabilities can’t be reactive. Proactive security is a must. Preventing data breaches from happening could mitigate undesired economic and political ramifications. The millions of daily, increasingly complex, cyberthreats speak to the opportunity for cybersecurity companies to continue to see greater demand for their services. Given its central role in protecting firms, consumers, and government bodies around the world, cybersecurity seems positioned to capitalised on more robust security and privacy measures and policies.
This document is not intended to be, or does not constitute, investment research